[top] Download Immunity Debugger Review
The query also carries an inherent anxiety. Debuggers, by their nature, require kernel-level hooks and driver installations. A modern user downloading Visual Studio Code has no fear; a user downloading a debugger fears rootkits, false positives from antivirus, and the dreaded "symbols not loaded" error. "Download" is a hopeful verb, but in this context, it is always followed by a silent prayer that the binary isn't poisoned. Herein lies the tragedy of the essay. If you type "download immunity debugger" into a search engine today, you will find a labyrinth of broken links, outdated forums, and conflicting advice. Immunity Debugger is, for all practical purposes, a dead project.
To "download Immunity Debugger" is an archaeological act. It is a recognition that in the fast-paced world of technology, even the most powerful tools are eventually reduced to a nostalgic search query. The download is not about getting the software; it is about preserving the methodology. The debugger is dead. Long live the debugging.
Its killer feature was the – a series of built-in analysis commands (like !findantidep or !pvefindaddr ) that automated the tedious grunt work of exploit development. If you were writing a zero-day exploit for a Windows service in 2010, you likely had Immunity Debugger open on one monitor and a hex editor on the other. Part II: The Query as a Ritual – Why "Download"? The inclusion of "download" is deceptively specific. Why not "install" or "use"? The word "download" implies a journey, a retrieval from a repository. It suggests that the user is not in possession of the tool and needs to acquire it from an authoritative source.
You cannot download Immunity Debugger anymore. You can only download its ghost. And in that ghost, you will find the limitations of a bygone era: no dark theme, no x64 support, a Python 2.7 dependency that will clash with your modern system. But you will also find a pedagogical clarity that modern, bloated tools lack.
In the era of Windows XP and early Windows 7, the dominant debuggers were OllyDbg (a user-friendly but closed-source tool) and WinDbg (a powerful but arcane beast from Microsoft). Immunity Debugger attempted to bridge the chasm. It grafted the intuitive, graphical interface of OllyDbg onto a Python-powered scripting engine. For the first time, a security researcher could write a Python script to automate the tracing of a buffer overflow, analyze heap structures, or even build rudimentary emulation layers directly inside the debugger.
They are not merely seeking a binary executable. They are seeking an education . They are seeking the specific, tactile experience of attaching a debugger to a vulnerable process, setting a breakpoint on strcpy , and watching the instruction pointer hijack into a JMP ESP gadget.
They are seeking access to a particular moment in hacker history—a time when Windows was a vast, uncharted continent of memory corruption, and a single debugger was the map and the compass.
In the peak years of Immunity Debugger (2008–2014), downloading it was a rite of passage. The official site required registration. Warez sites hosted cracked versions. GitHub did not yet dominate the tooling landscape. To "download Immunity Debugger" was to perform a small act of rebellion: you were pulling a piece of professional-grade exploit development software onto your local machine, often bypassing corporate IT policies or university firewalls.
[top] Download Immunity Debugger Review
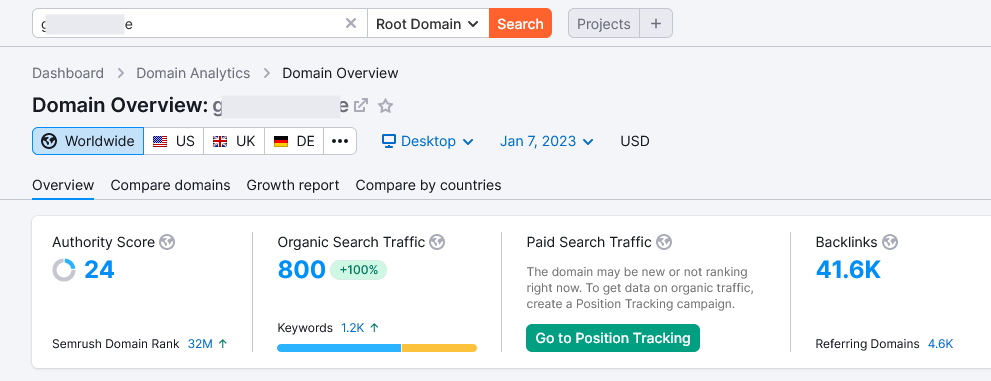
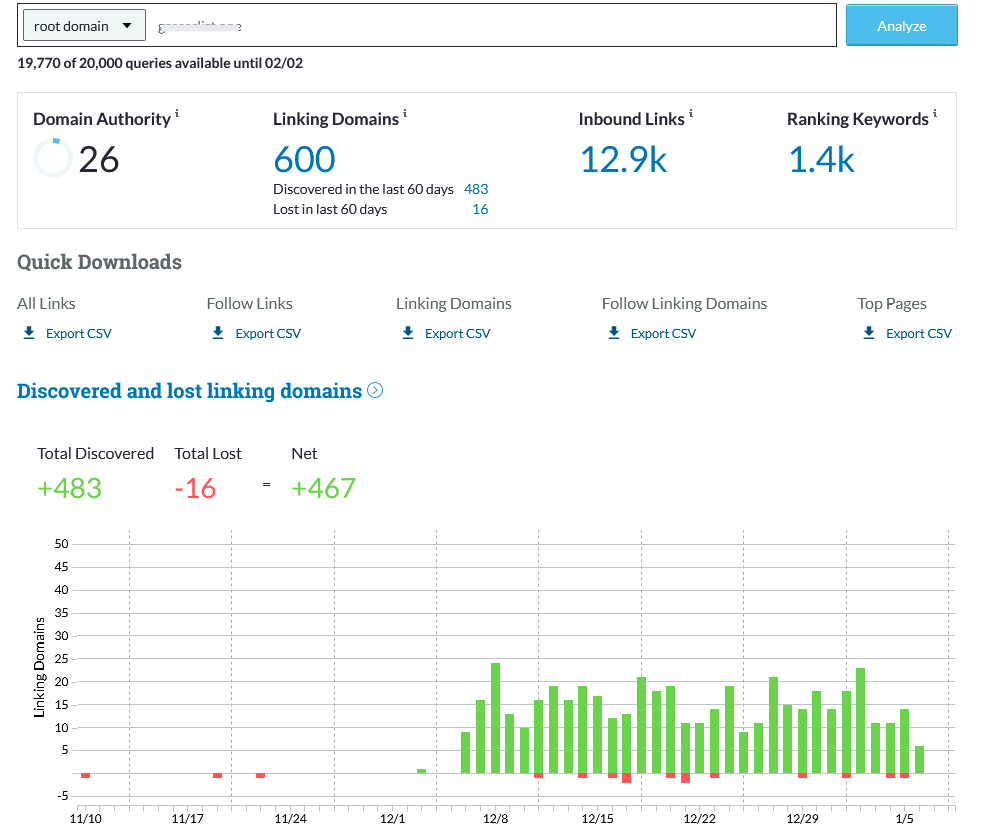
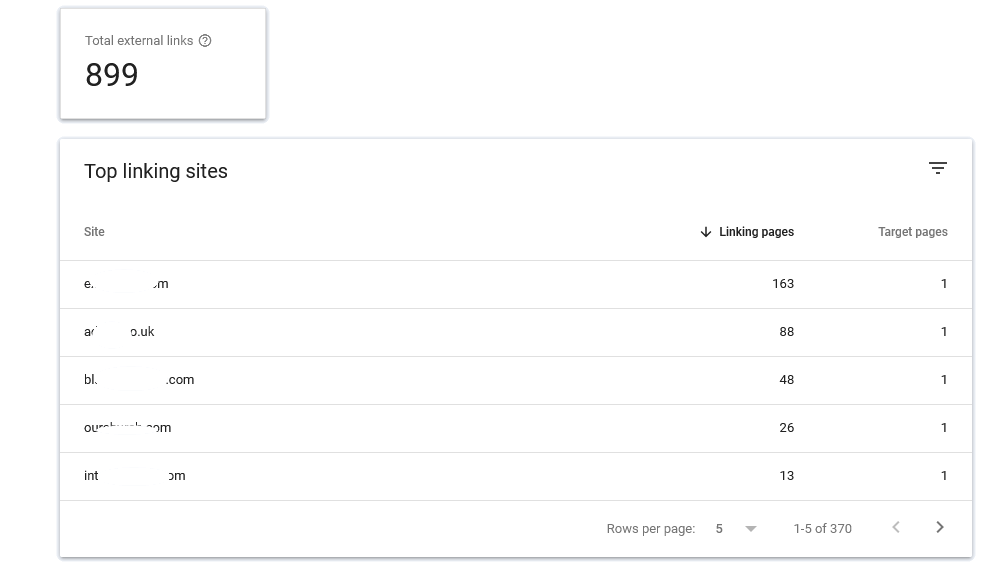
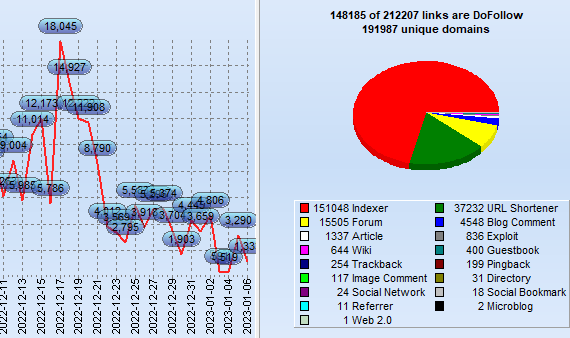
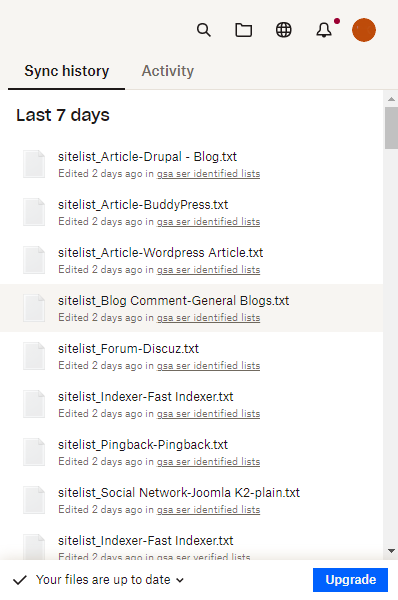
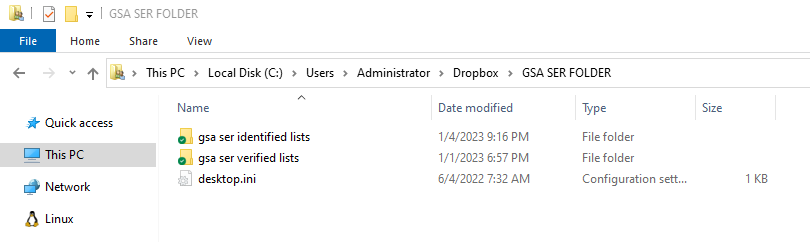
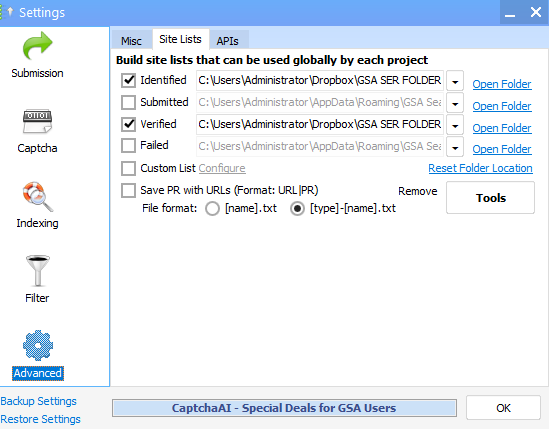
What exactly is GSA SER Verified List? And What is the best way to rank on It?
GSA Search Engine Ranker (SER) is an effective tool utilized by SEO professionals to create high-quality
link opportunity for their websites.
With GSA SER, marketers are able to quickly develop an inventory of verified hyperlinks that are
specifically tailored to the specific requirements of their clients. This allows them to concentrate on
those that are relevant and achieve the most effective outcomes.
Benefits of Using a GSA SER Verified List
The use of the GSA verified list for SER enables marketers to quickly and effortlessly identify top-quality
link building opportunities that can improve their rankings on search engine result page (SERPs).
download immunity debugger
It is constantly updated continuously to ensure that marketers can be assured that they are receiving the
most recent information available. Furthermore, many of the websites listed on the list are from sites that
are low-OBL Tier 1 This means they are more likely to attract high traffic and aid your blog or website to
climb up the ranks.
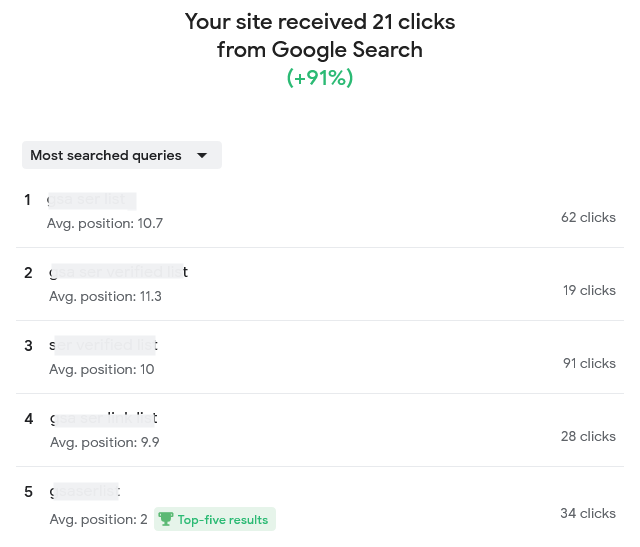
How Do You Improve Your Ranking by using the help of a GSA Verified Lists of SERs?
Once you've found opportunities to build links from the GSA SER verified list, it's crucial to concentrate
on creating content of high quality that is engaging for users and ultimately get them clicking on your site
or blog.
The query also carries an inherent anxiety
Making informative, useful and relevant content can help you get higher rankings on the results pages of
search engines by demonstrating to Google that your website is an authority in the topic. It is also
important to ensure that all links link back to your site or blog, since this will provide Google the
impression of trustworthiness and relevancy when it comes to ranking.
What Are Some Best Practices When Using a GSA SER Verified List?
If you are using a GSA SER verified list, bear in your mind that when you are looking at link opportunities
for building quality must always take priority over the quantity. In addition, focusing on generating
articles that are valuable to users rather than trying to build the most links possible will ensure higher
rankings in the long run.
"Download" is a hopeful verb, but in this
Not last, you should be careful not to overuse keywords overly often to prevent your website from being
considered low-quality or spam and causing your rankings to drop instead of increasing.
Conclusion: SER Verified List
Utilizing the GSA SER list will offer SEO professionals with top-quality link
building options specifically to their requirements that can result in better rankings for their site or
blog over time, if followed correctly, following best practices, such by focusing on the creation of
high-quality content, not quantity, as well as avoiding keyword stuffing and so on.
In the end making use of this tool in the right way will allow you to achieve higher results in search
engine optimization more quickly than ever before!
Order Now
The query also carries an inherent anxiety. Debuggers, by their nature, require kernel-level hooks and driver installations. A modern user downloading Visual Studio Code has no fear; a user downloading a debugger fears rootkits, false positives from antivirus, and the dreaded "symbols not loaded" error. "Download" is a hopeful verb, but in this context, it is always followed by a silent prayer that the binary isn't poisoned. Herein lies the tragedy of the essay. If you type "download immunity debugger" into a search engine today, you will find a labyrinth of broken links, outdated forums, and conflicting advice. Immunity Debugger is, for all practical purposes, a dead project.
To "download Immunity Debugger" is an archaeological act. It is a recognition that in the fast-paced world of technology, even the most powerful tools are eventually reduced to a nostalgic search query. The download is not about getting the software; it is about preserving the methodology. The debugger is dead. Long live the debugging.
Its killer feature was the – a series of built-in analysis commands (like !findantidep or !pvefindaddr ) that automated the tedious grunt work of exploit development. If you were writing a zero-day exploit for a Windows service in 2010, you likely had Immunity Debugger open on one monitor and a hex editor on the other. Part II: The Query as a Ritual – Why "Download"? The inclusion of "download" is deceptively specific. Why not "install" or "use"? The word "download" implies a journey, a retrieval from a repository. It suggests that the user is not in possession of the tool and needs to acquire it from an authoritative source.
You cannot download Immunity Debugger anymore. You can only download its ghost. And in that ghost, you will find the limitations of a bygone era: no dark theme, no x64 support, a Python 2.7 dependency that will clash with your modern system. But you will also find a pedagogical clarity that modern, bloated tools lack.
In the era of Windows XP and early Windows 7, the dominant debuggers were OllyDbg (a user-friendly but closed-source tool) and WinDbg (a powerful but arcane beast from Microsoft). Immunity Debugger attempted to bridge the chasm. It grafted the intuitive, graphical interface of OllyDbg onto a Python-powered scripting engine. For the first time, a security researcher could write a Python script to automate the tracing of a buffer overflow, analyze heap structures, or even build rudimentary emulation layers directly inside the debugger.
They are not merely seeking a binary executable. They are seeking an education . They are seeking the specific, tactile experience of attaching a debugger to a vulnerable process, setting a breakpoint on strcpy , and watching the instruction pointer hijack into a JMP ESP gadget.
They are seeking access to a particular moment in hacker history—a time when Windows was a vast, uncharted continent of memory corruption, and a single debugger was the map and the compass.
In the peak years of Immunity Debugger (2008–2014), downloading it was a rite of passage. The official site required registration. Warez sites hosted cracked versions. GitHub did not yet dominate the tooling landscape. To "download Immunity Debugger" was to perform a small act of rebellion: you were pulling a piece of professional-grade exploit development software onto your local machine, often bypassing corporate IT policies or university firewalls.